
The writer Paul Maguire is the co-founder and CEO of Knowmadics. He is a former intelligence officer with multiple deployments to the Persian Gulf and Southeast Asia.
Affordable LiDAR sensors, artificial intelligence-enabled analytics, and cloud platforms have turned 3D sensing into a shared capability across allies and adversaries. For security professionals, the challenge is maintaining decision advantage in an environment where both defenders and adversaries can see in three dimensions.
Space-based LiDAR offers extraordinary detail, unparalleled terrain characterization, foliage penetration, and elevation modeling across vast regions. Security and defense organizations use these datasets to identify infiltration corridors, analyze terrain masking for movement, detect new construction, and detect subtle changes, such as tunnel entrances or excavation sites.
A recent research paper from Carnegie Mellon University demonstrated a method for long-distance GPS-denied navigation by using LiDAR measurements matched against a prior digital elevation model. This technique achieved a final position error of only 27 meters over a 218 kilometer flight. Persistent orbital coverage, coupled with change detection algorithms, also makes it possible to identify small ground shifts that once went unnoticed.
Commercial providers now distribute dense elevation models and LiDAR-derived terrain products to customers worldwide. State and nonstate actors can acquire the same data products to improve targeting, camouflaging, or route planning. Criminal and extremist groups may use them to move contraband through under-observed corridors or to plan operations in terrain poorly covered by traditional surveillance. The advantages go to the side that integrates high resolution LiDAR derived models and protects them best.
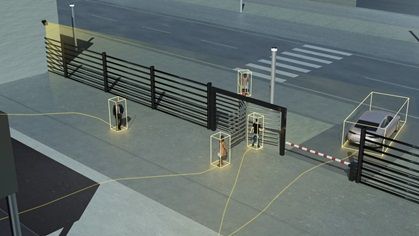
At the tactical level, LiDAR has become transformative. Ground-based LiDAR is now a standard tool for precision mapping. Handheld scanners, helmet-mounted units, indoor robots, and small unmanned aircraft can generate detailed 3D maps of jungles, urban areas, and GPS-denied interiors. These tools improve planning and reduce uncertainty by identifying disturbed ground, hidden structures, or micro-terrain features that affect movement and safety.
Commodity LiDAR sensors now exist in smartphones, drones, and robotics toys. They are easy to access and cheap options to map a facility’s perimeter, identify blind zones, or model the terrain surrounding a convoy or secure compound. Indoors, adversaries can map high-value facilities to support assaults or hostage operations.
 Across both orbital and terrestrial domains, LiDAR’s accessibility has erased the traditional divide between professional security forces and their adversaries. Once reserved for advanced military programs, this technology now exists in commercial satellites, consumer drones, and public cloud platforms. The challenge for defenders is no longer obtaining data but securing it and interpreting it faster and more effectively than those who would exploit it.
Across both orbital and terrestrial domains, LiDAR’s accessibility has erased the traditional divide between professional security forces and their adversaries. Once reserved for advanced military programs, this technology now exists in commercial satellites, consumer drones, and public cloud platforms. The challenge for defenders is no longer obtaining data but securing it and interpreting it faster and more effectively than those who would exploit it.
The most profound shift lies not in collection, but in interpretation and exploitation. Modern cloud platforms now offer artificial intelligence-based (AI-based) automation and capabilities that include:
- Point cloud cleaning and noise removal
- Object detection and automated labeling
- Structure and floorplan extraction
- Route analysis and choke-point identification
- Virtual walk-through generation
- Export of ready-to-use analytic products
This AI-enhanced environment supercharges analysis time. Raw scans from a handheld device or drone can be uploaded and transformed into a highly refined operational picture within minutes, improving situational understanding and coordination.
For protective intelligence teams, such automation can reduce the delay between reconnaissance and actionable insights, allowing faster response to emerging threats. The burden on analysts shrinks and decision cycles tighten.
An example of a scenario where this technology could have been used to identify and respond to a tactical threat would be the 2024 assassination attempt on then U.S. presidential candidate Donald Trump. Pre-event site preparation coupled with AI enhanced exploitation tools from multiple well-known commercial geographic information system vendors could have easily identified elevated positions with lines of sight to locations that a principal is going to traverse.
LiDAR used in that scenario could have easily highlighted the areas that needed to be reviewed, cordoned off, and surveilled/monitored before the president’s campaign appearance. Applying this approach in the future would help with resource allocation decisions pre-event and support situational awareness efforts during an event.
 LiDAR data also enables adversaries to create realistic rehearsal environments and autonomous flight paths for uncrewed systems. Three-dimensional models of targets allow for virtual mission planning and practice. Drones can be trained to navigate without GPS, allowing them to operate in areas where satellite signals are blocked or jammed.
LiDAR data also enables adversaries to create realistic rehearsal environments and autonomous flight paths for uncrewed systems. Three-dimensional models of targets allow for virtual mission planning and practice. Drones can be trained to navigate without GPS, allowing them to operate in areas where satellite signals are blocked or jammed.
Traditional counter-drone systems that rely on radio frequency (RF) or GPS signatures struggle against LiDAR-guided drones that fly silent, low-profile, terrain-hugging routes with no RF emissions until terminal approach.
Security professionals must now treat LiDAR as a permanent feature of operational risk.
Maintaining awareness and control to mitigate and/or exploit LiDAR requires three priorities:
- Integration. Security practitioners need to partner with data scientists, IT experts, and intelligence analysts to unify varied sensor outputs. Combining LiDAR data with thermal, RF, and hyperspectral imagery requires expertise in data fusion, network management, and deep analysis to create a comprehensive view. Fortunately, there are commercial tools available to automate that. Unfortunately, adversaries have access to many of those same tools.
- Signature management. Facilities, engineering, and camouflage experts will be needed to reduce system appearance in scans. There are several well understood analog techniques to include absorbing materials, angled and irregular facades, and other techniques to interfere with the Time-of-Flight characteristics that make LiDAR so precise. Assessing and altering the physical appearance of assets (using screening, deception, lighting) to defeat accurate LiDAR reconstruction requires input from those who build and maintain the sites.
- Counter-mapping tactics. Airspace security, cyber, and legal teams must partner to detect, disrupt, and regulate unauthorized collection of 3D data by drones or ground devices. All three teams will need to work together to disrupt these efforts and set the legal framework for detection and response protocols.
LiDAR’s accessibility cannot be reversed. The advantage will go to organizations that process it faster, integrate it more effectively, and protect its signatures with discipline and intent.











